Coinmarketcap tutorial deutscherste schritte in kryptowahrung blockchainbitcoin ethereum
44 comments
Bitcoin asics for sale
A survey on security and privacy issues of Bitcoin Conti et al. At the core of this survey is a catalogue of security attacks on Bitcoin, together with known defences or mitigations where applicable.
A double spending attack occurs when the same set of bitcoins are spent in two different transactions. It involves arranging things so that a vendor sees a transaction confirmation and releases the product , but a double-spend transaction e.
Thus the attackers has the goods and the coins. The Finney attack is a form of double spending attack in which a dishonest client pre-mines a block containing a transaction paying the coins to an address under their control.
On successfully mining such a block, the attacker creates and submits a transaction paying the same bitcoins to a vendor. Once the vendor receives confirmation that the transaction is valid and included in the blockchain, the attacker immediately releases their pre-mined block, creating a fork of equal length to the existing fork. The attack succeeds if the attackers fork becomes the prefix of the longest chain.
With more compute power e. The rest of the attack proceeds as for Finney, but the attacker releases the whole block sequence once the vendor has received a transaction confirmation, thus immediately becoming the longest chain. A dishonest client with a pre-mined block can also perform a vector 76 double spending attack.
The main difference is that the target is an exchange rather than a vendor. The pre-mined block contains a deposit transaction moving funds to an exchange. If the deposit fork is ultimately thwarted, then the deposit never happens. In the meantime, the attacker may have been successful in withdrawing the funds and the exchange is out of pocket. Based on the above discussion on double spending attack and its variants, one main point that emerges is that if a miner or mining pool is able to mine blocks with a faster rate than the rest of the Bitcoin network, the possibility of a successful double spending attack is high.
And the most effective way to do that is to wait for multiple numbers of confirmations e. The classic bitcoin client only shows a transaction as confirmed after it is six blocks deep. In fast payment scenarios where it is not desirable to wait that long, we can increase the vendor confidence if we can detect double-spending attempts within a shorter time window. At its most basic, the vendor chooses a listening period and monitors all broadcast transactions during this period.
The product is only delivered if no double spend transaction is detected in this time. If the vendor has access to a number of observer nodes in the network, this increases the probability of detecting the transaction. Alternatively, if miners were to automatically forward any double spend attempt they detect instead of just discarding the transaction this would also increase the probability of timely detection.
Other proposals involve setting up various forms of escrow with misbehaving parties losing their funds upon detection. For now, it is safe to conclude that there is no solution available in the literature that guarantees the complete protection from double spending in Bitcoin. The existing solutions only make the attack more difficult for adversaries. In particular, double spending is an attack that is well discussed in the Bitcoin community, but very few solutions exist so far, and it remains an open challenge for researchers.
When the motivation is not to profit directly through Bitcoin, but instead to bring down the currency or network, it is called a Goldfinger attack. Internal attacks are those in which miners act maliciously within the pool to collect more than their fair share of collective reward or disrupt the functionality of the pool to distance it from successful mining attempts.
In external attacks, miners could use their higher hash power to perform attacks such as double spending. In block discarding, a dishonest miner or colluding set of miners working in a pool withholds a block once found.
They keep working on the private chain, while the rest of the miners work on the shorter public chain. If the dishonest subset can maintain a lead on their branch they will gain proportionally more rewards as the rest of the miners are wasting their efforts — effectively reducing their compute power.
If the dishonest and honest forks get back to the same length, the dishonest miners publish their mined blocks immediately. If this becomes the longest chain, they win! Block withholding is an internal attack on a mining pool, which could be by infiltration from a rival pool. In this way it is possible either to undermine a rival pool, or potentially to profit directly via similar race-to-publish schemes as we have seen before.
The Miners Dilemma shows that if two pools attack each other this way they arrive at a Nash Equilibrium in which each earns less than they would have if neither of them attacked. The fork after witholding variation though does not have this disadvantage and can be used up to four times more often per pool than a straightforward block withholding attack. See my earlier post for a description of how it works.
As well as being more profitable, there is no known defence at the moment. Power loves to concentrate. Beyond the major attacks summarised above, there are also a number of techniques and bad behaviours that can be used to disadvantage participants in the network.
These are summarised in table II:. An attacker obtains a majority of computing resources for a duration via bribery. Several bribing schemes have been discussed included out-of-band payments, setting up mining pools with higher reward payments to lure miners, and creating forks with bribe money available to any miner adopting them.
Once hash power is temporarily enhanced, other attacks such as those outlined above become more tractable. Refund attacks target the BIP70 payment protocol governing how vendors and customers perform payments in Bitcoin.
In punitive forking the goal is to blacklist or censor Bitcoin addresses owned by certain people e. This works when the attacker has the majority of the hash power. The attacker announces that they will not extend any chain containing blacklisted transactions, and immediately forks and creates a longer chain if blocks containing such transactions do appear. In feather forking the attacker announces a similar intention, but also that they will give up attempting to fork after a while say falling k confirmations behind the main chain.
Other miners are still motivated to block blacklisted transactions because they increase the probability the miner will lose their reward.
An attacker performing feather forking can also use it to blackmail a client by threatening that all her transactions will be put on the blacklist until the client pays the asked ransom coins. Transaction malleability refers to a bug in the original protocol but not the reference implementation through which it is possible to change the redeem script in a transaction without invalidating the signature. Several exchanges were vulnerable to this. One of the most straightforward attacks.
Find the owner of a high value address and steal or destroy their private key. All participating nodes in the Bitcoin network maintain a time counter representing network time. If the median time differs by more than 70 minutes the system time, the network time counter reverts to system time.
Attempting to disrupt network access for target miners, effectively taking them out of the Bitcoin network. Such attacks seem to be widespread in practice. Installing lots of dummy helper nodes false identities and using them to try and compromise a part of the network. Forcing a network partition between a victim and the public network. IP addresses to which the victim connects are diverted towards an adversary. Coupled with the ability to trace the history of every coin, this has some interesting currency implications:.
The fact that the transaction history of each bitcoin is traceable puts the fungibility of bitcoins at risk… No two coins are equal, and fungibility, a fundamental property required in every currency, is at risk. You are commenting using your WordPress. You are commenting using your Twitter account. You are commenting using your Facebook account. Notify me of new comments via email. Notify me of new posts via email. Double spending attack A double spending attack occurs when the same set of bitcoins are spent in two different transactions.
There are several schemes for achieving a favourable fork, starting with the Finney attack. Finney attack The Finney attack is a form of double spending attack in which a dishonest client pre-mines a block containing a transaction paying the coins to an address under their control.
Brute force attack With more compute power e. Discussion Based on the above discussion on double spending attack and its variants, one main point that emerges is that if a miner or mining pool is able to mine blocks with a faster rate than the rest of the Bitcoin network, the possibility of a successful double spending attack is high.
The following chart shows the market share of hashrate for mining pools as of December Again, the best defence is patience! Waiting for more confirmations.
Block withholding Block withholding is an internal attack on a mining pool, which could be by infiltration from a rival pool. Fork after withholding The fork after witholding variation though does not have this disadvantage and can be used up to four times more often per pool than a straightforward block withholding attack.
These are summarised in table II: Bribery attacks An attacker obtains a majority of computing resources for a duration via bribery.
Refund attacks Refund attacks target the BIP70 payment protocol governing how vendors and customers perform payments in Bitcoin. Punitive and feather forking In punitive forking the goal is to blacklist or censor Bitcoin addresses owned by certain people e. Transaction malleability Transaction malleability refers to a bug in the original protocol but not the reference implementation through which it is possible to change the redeem script in a transaction without invalidating the signature.
Wallet theft One of the most straightforward attacks. Time jacking All participating nodes in the Bitcoin network maintain a time counter representing network time. DDoS Attempting to disrupt network access for target miners, effectively taking them out of the Bitcoin network. Sybil Installing lots of dummy helper nodes false identities and using them to try and compromise a part of the network.
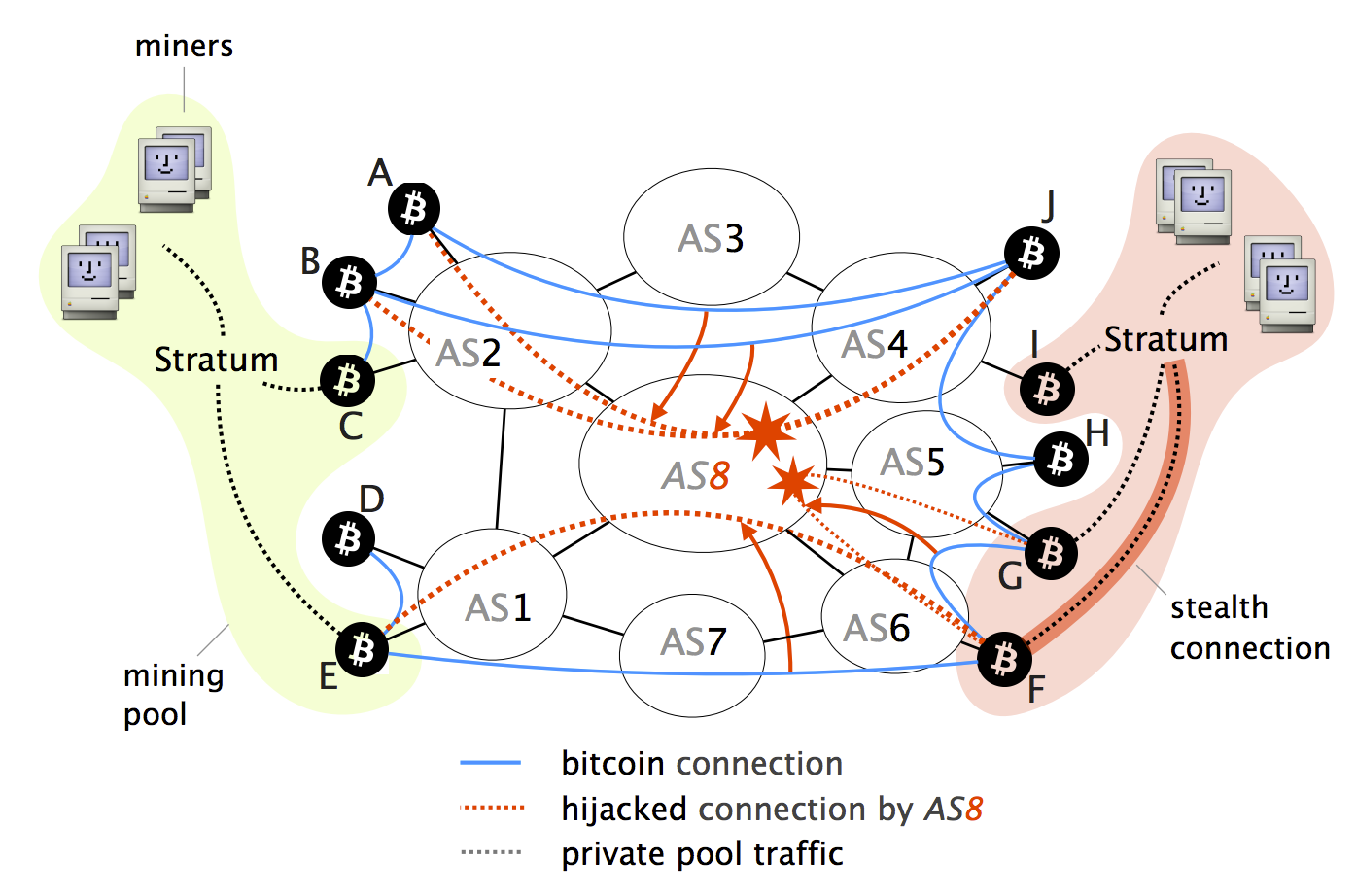
Eclipse or netsplit Forcing a network partition between a victim and the public network. Tampering Introducing network delays in the broadcast of blocks and new transactions. Routing attacks Using e. Coupled with the ability to trace the history of every coin, this has some interesting currency implications: Twitter LinkedIn Email Print.
Leave a Reply Cancel reply Enter your comment here Fill in your details below or click an icon to log in: