Uk blockchain wiki
41 comments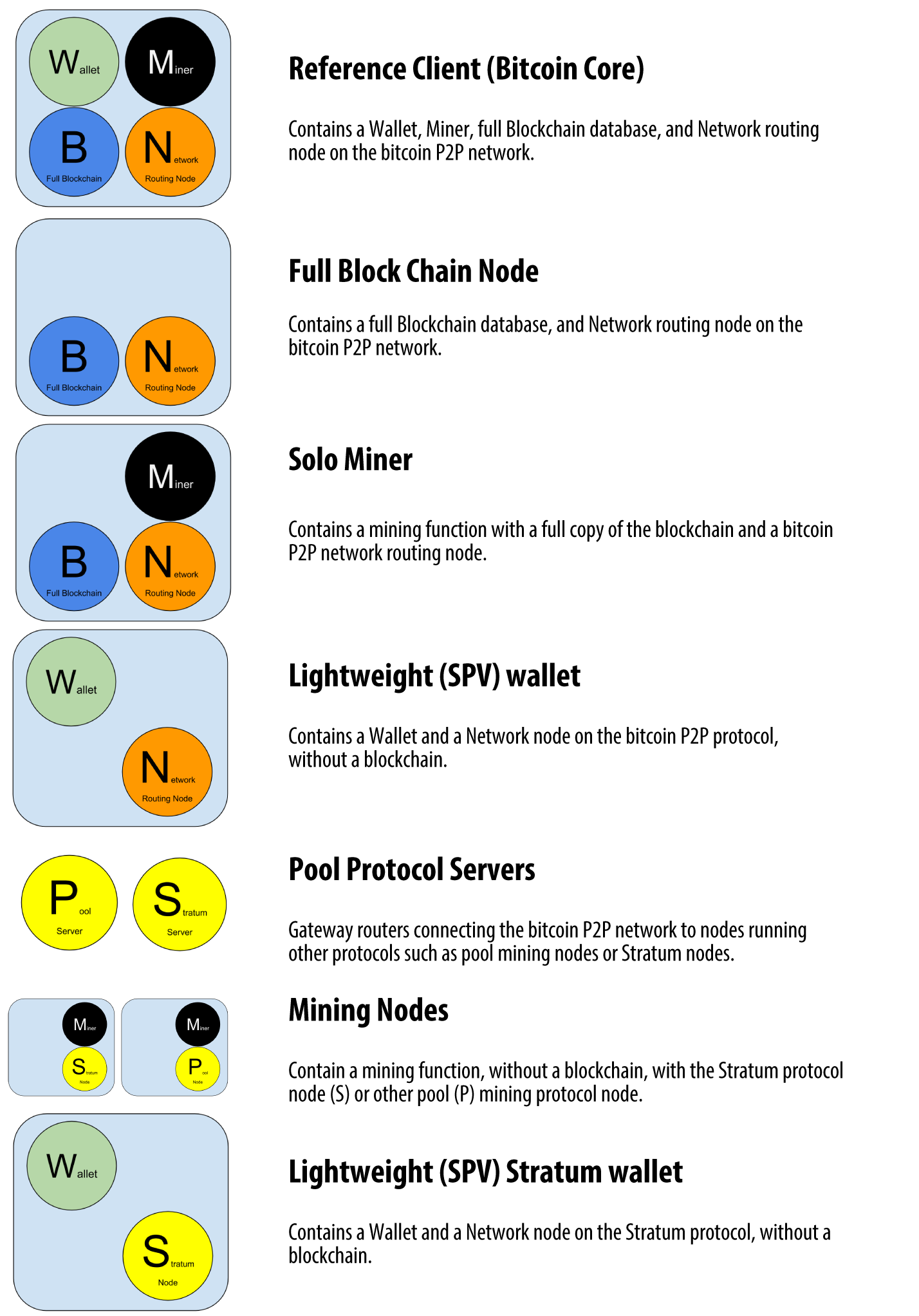
Bitcoin mining hash rate chart
Replace transaction merkle tree with a Merkle-sum-tree. This allows SPV nodes to stochastically validate the subsidy in blocks by fetching a random leaf and then fetching its txins. This way if you have a stream of utxo queries coming in, you can make the work of them mine for you. Validation then, is mining. If you don't have enough queries coming in you just make some up at random. Represent the script as a merklized abstract syntax tree.
The P2SH address is the root. When spending the spender only may provide only the branch they are executing, and hashes for the unexecuted branches.
This increases privacy and can compress long scripts on spend. Pruned history Structure transactions so that the parts needed for validation txins, scriptsigs are separate from the output data scriptpubkey, output and fee values and put them in separate hash trees.
All nodes fully prune all data more than a few thousand blocks back. Massive space savings and improvements in syncup speed.
Massive security loss— an attacker that can construct a large reorg can steal all the transacted coin beyond a certain depth. Normative and committed merklized UTXO data structure allows full validation of current blocks by storageless nodes with SPV security Can be complimented by proof-of-misbehavior messages that show a block is invalid by packing up the tree fragments that provide the data needed to see its invalidity. ZKP Validated checkpoints— Is it possible to use computational integrity to create compact constant size checkpoint proofs that show that a checkpoint was the result of a faithful validation of the blockchain?
This could be used to give pruned history the same security as full Bitcoin up to the limitations of the integrity proofs. Chain folding If nodes don't actually need to validate old chain data because of committed UTXO and pruned history , it would be possible to 'fold up' the historic chain: Nodes which are validating just to gauge difficulty can skip the intermediate blocks.
This can be applied recursively. If the backpointers are randomized and every block is a candidate summary you end making the chain a merklized skiplist. Alternatively, do not store a UTXO set. Instead encode the transactions outputs in the blockchain in a merkle mountain range an insertion ordered fully populated binary tree, setup to make appends cheap over the whole chain.
Transactions are required to provide the update proofs that show their inputs in the tree and thus also allow you to null them out. This means that fully validating nodes and miners can be basically storageless, but wallets must take on the cost of remembering their own coins. A transaction is mined but it isn't clear which inputs its spending. Fees are paid by unblinded inputs to prevent DOS attacks. Blinding is done in such a way that double spends are still obvious.
If full nodes become expensive to operate in the future then they may become uncommon and this could compromise the security of Bitcoin. This risk can be reduced if it's made possible for Bitcoin nodes to check all the rules at random and transmit compact proofs of rule violations. If this is done even if there is only one honest full node in the world the system is secure so long as it can communicate to all others.
In general, in any deterministic computation process if you have simple state updates and commit to the sequence of states a compact proof of invalidity can be generated by producing a hash tree fragment to the first invalidate state transition. Ideas in this space have been previously discussed under the banner of proof-of-treachery [1]. Right now not all of the rules can be checked randomly or have compact proofs. SPV header checks — time, target, difficulty, already have them. But if future SPV nodes don't really check all the headers in the future it may be useful to arrange old header times in a merkle mountain range to proofs of sum difficulty and compact proofs of incorrect difficulty.
Proof of invalid script Possible in the current system: Proof is tree fragments for the invalid txn in question as well as one invalid input no need to include more than one. Could be made more efficient by including commitments to intermediate states, but with the opcode limit all scripts are compact to verify in Bitcoin without doing anything fancier. Also proves nlocktime, etc. To prove output value greater than inputs all inputs must be provided in the proof.
Proof of double spend Possible in the current system: Proof is tree fragments for the two transactions which spend the same input. Proof of false inflation Not possible without more data: The coinbase payment is the sum of fees in a block and the subsidy.
Fees require knowing the transaction's inputs output values, to check subsidy you must not only have all the transactions but all their inputs as well.
Nodes can randomly check this by grabbing a random txn and checking its inputs, and compactly prove violation by showing where the fees don't match their commitments. Proof of block too large Similar to false inflation, requires all the transactions, can similarly be solved by including the sum of txn sizes in the tree. Proof of spending a non-existing input Requires additional data: Proof is a pair of tree fragments for the higher and lower records for the missing entry, and another pair for the outputs created within a block but consumed.
I think you can even pull that off as a soft-fork I get your point, sometimes just trust-less is enough I think the big question is do you need the self-modifying code that forth makes possible? IE things like SPV-verifiable colored coins I think it makes most sense when the only pow is in tx's, although exactly what that'd look like is an interesting question I'd still be in favor of improving things generally, e.
What I'd do is just implement a generic snark validation, and providing the snark verification key in the transaction. Though I'm not aware of any way to do that which we'd consider in scope for this discussion. I propose that if our choice operator s are good then a maximally efficient winternitz signature will be completely natural.
The public key is just the root hash over this data. So, is there a way with ECDSA, given three messages pick a pubkey,r,s such that pubkey,r,s is a valid signature of any one of the three messages?
I think the most fundemental thing I've discovered is the concepts of how mining can be separated into timestamping and proof-of-publication Is it back in your possession now? What if that data has been further split into multiple parts with an error correcting code and spread to multiple machines. Now where does the coin reside? But there is no need that the best analogies need to be physically intutive, in fact basically all of higher mathmatics is about manipulating abstractions which are in no way physically intutive.
I think relating to a payments ability to require transferable restrictions on the next transaction. But make the covenants temporary, the coins themselves perishable, or applied to user issued assets not colored coins but separately issued assets a la freimarkets , and it is a different story IMHO.
Some of your competition doesn't mind disclosing this however. I think they should just take the scheme we discussed previously and execute it under a ZKP for general programs. It would be similar in size to the zerocash proofs. Verifer does this too. Both prover and verifier get a hash root. The verifyer verifies the signature and the zkp.
But it shouldn't be terrible. I believe it would be cheaper than another sha hash in any case. Or of an encrypted value or..
I think not, at least not with the GGPR12 stuff as the arith circuit field size is set by the size of the pairing crypto curve. You could get more elaborate, like timelocking the funds and show that funds beyond the withdraw daily limits are actually unspendable by the network, but perhaps I'm getting to cipherpunk there. I'm thinking for a merklized AST what makes sense is merklized forth.
The forth dictionary concept is perfect for it, and means you have a simple, easy to implement language already used for embedded andother things and bitcoin scripting along with all the usual nice things like editor modes and what not So you've got your parameter stack and return stack, and are thus at the point where you can recreate Bitcoin scripting.
Now the interesting thing to do is add TPM functionality, which means a PCR opcode and stack to allow you to select what you want to consider as the start of the current trusted block of code.
Then add an encrypted stack, as expected encrypted with H sec PCR tip , and some sort of monotonic counter thing. That should give you enough to do trusted computing with an extremely stable API, and that API itself can be just AST heads of useful library function calls that may actually be implemented directly in C or whatever rather than the opcodes themselves. I don't know that explicitly supporting that makes sense.. Equally, forth is already common in applications, IE spacecraft, where you need relatively bare metal languages with simple frameworks and symantics; note how with forth it's much easier to get to the level where you trust that the code being run is what you actually wrote than, say, C.
Equally, forth is already common in applications, IE spacecraft, where you need relatively bare metal languages with simple frameworks and symantics; note how with forth it's much easier to get to the level where you trust that the Just be clear what the maximum's are for the variou parts of the stack.
Dunno yet what the stack datatype should be, MPI's are nice but there is the subtle issue that it'd be good to have some clear idea of how many operations an operation takes. Of course, really simple would be bit ints and implement everything higher level in forth. Maybe a merkle mountain range of every value ever associated with a given key?
I mentioned to TD earlier today the idea of miners committing to a merkle tree of txids in their mempool, just to prove visibility, you could use that if the commitment included txins being spent.
Appending needs to touch only the "mountain tips", that is the perfect merkle trees already stored, and for n items stored you'll have log2 n trees.
I've got an idea where you'd make transactions have commitments of previous ones with a merkle-mountain-range-like scheme so you could efficiently reference any previous transaction up to the genesis block. This is easiest to understand if transactions can only have linear history, but a dag history is doable too. Anyway, wallet software would receive that history to know the coins are valid, thus pushing validation directly to the users. Obviously some way of pruning that history is important, SCIP is heavy-weight and complex but could work.
So one possible accumulator would be to construct a merkle tree of a bit field with one bit for every integer between 0 and 2 You can prove you added an integer to that set by showing the leaves for an operation updating the appropriate bit, and you can remove an integer with another set of leaves.