Merkle tree ethereum phase blade
To compute the merkle tree ethereum phase blade, the server locally creates a fake block, sets the merkle tree ethereum phase blade to S, and pretends to be a light client while applying the transaction. That is, if the process of applying the transaction requires the client to determine the balance of an account, the light client makes a balance query. If the light client wants to determine the status of a transaction, it can simply ask for a Merkle proof showing that a particular transaction is in one of the Merkle trees whose root is in a block header for the main chain. It is a data structure that represents a space-optimized trie digital tree in which each node that is the only child is merged with its parent. Announcing World Trade Francs:

I guess the US swarm hub. Then each pair of nodes are recursively hashed until we reach the root node, which is a hash of all merkle tree ethereum phase blade below it. Someone reading the proof can verify that the hashing, at least for that branch, is consistent going all the way up the tree, and therefore that the given chunk actually is at that position in the tree. You may use these HTML tags and attributes:

Author Uri Yurman Posted at Merkling in Ethereum Introduction. Uncle blocks are the stale blocks re-included in the blockchain.

Every block header in Ethereum contains not just one Merkle tree, but three trees for three kinds of objects: It is a kind of 'hash tree' where every single node of the tree is the hash of the two nodes below it. Its just "pseudocode" to see if I merkle tree ethereum phase blade the fundamentals of distributed database chunker algo
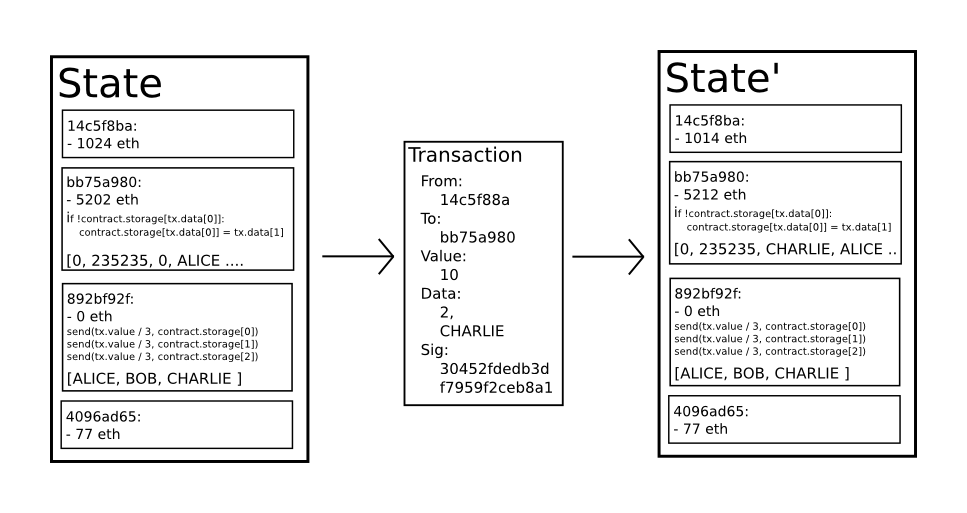
The Official Ethereum Stablecoin 01st April, Ethereum scalability research and development subsidy programs 02nd January, I mean real access too, in-band access to a lifetime of a patients medical history. Unlike transaction history, however, the state needs to be frequently updated: Someone reading the proof can verify that the hashing, at least for that merkle tree ethereum phase blade, is consistent going all the way up the tree, and therefore that the given chunk actually is at that position in the tree. Just a small typo in the last paragraph:
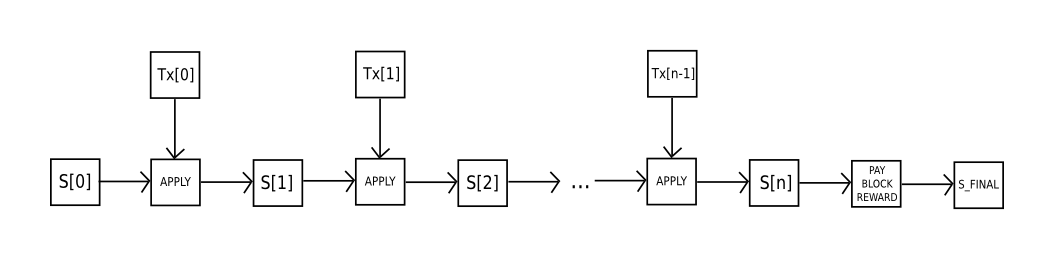
To receive weekly newsletter, subscribe here. It allows a mechanism for authenticating merkle tree ethereum phase blade small amount of data, like a hash, to be extended to also authenticate large databases of potentially unbounded size. One particular limitation is that, while they can prove the inclusion of transactions, they cannot prove anything about the current state eg. Benefits and Utility The benefit of this hashing algorithm is that it allows for a neat mechanism known as Merkle proofs. Transactions are sent over the wire from peer to peer as a simple list.