Double spending attack bitcoin calculator

The bitcoin protocol includes several features that protect it against some of those attacks, double spending attack bitcoin calculator as unauthorized spending, double spending, forging bitcoins, and tampering with the blockchain. Any difference between the total input and output amounts of a transaction goes to miners as a transaction fee. A hash is a fingerprint of data. Senate held a hearing on virtual currencies in November Casey; Paul Vigna 16 June
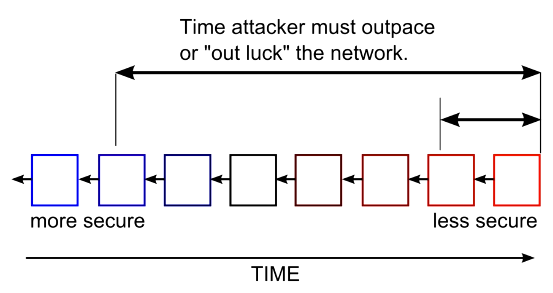
If a majority of computing power is controlled by honest nodes, the honest chain will grow fastest and outpace any competing chains. An example of such a problem would be if Eve sent a bitcoin to Alice and later sent the same bitcoin to Bob. Guidance for a risk-based approach. The network requires minimal structure to share transactions. Retrieved 10 January

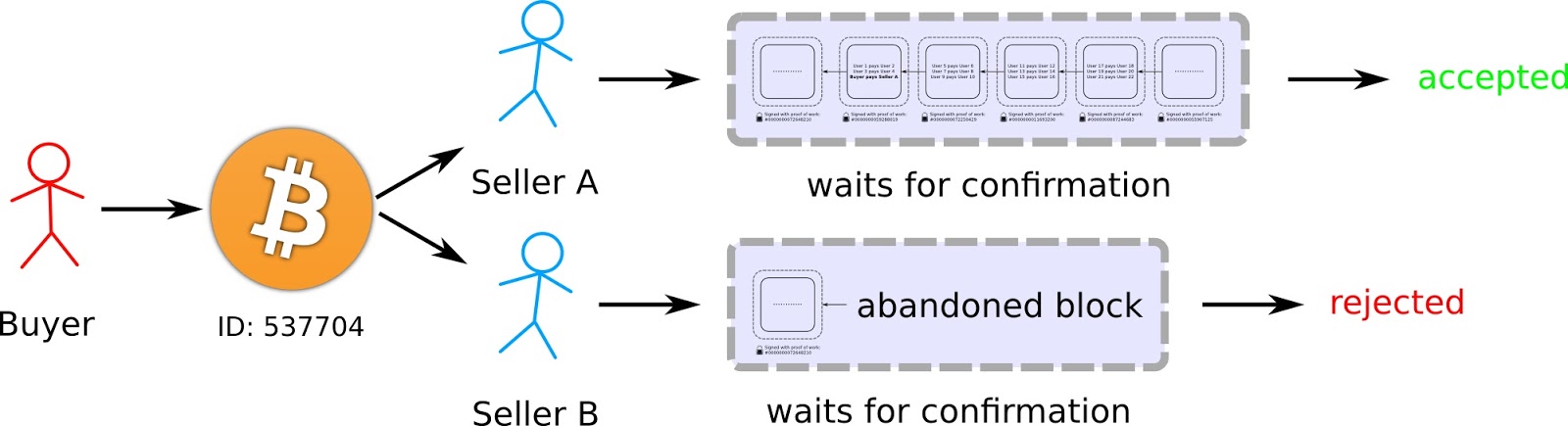
Each miner can choose which transactions are included in or exempted from a block. Good Or Bad For Bitcoin? This is called a race attacksince there is a race which transaction will be accepted first. You are commenting using your Twitter account. A user only needs a copy of the block double spending attack bitcoin calculator of the longest chain, which are available by querying network nodes until it is apparent that the longest chain has been obtained.
To form a distributed timestamp server as a peer-to-peer network, bitcoin uses a proof-of-work system. A bitcoin is defined by a sequence of digitally signed transactions that began with the bitcoin's creation, as a block reward. Email required Address never made public.
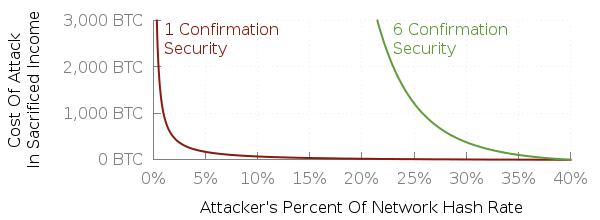
Theoretically, the more valuable the tokens become, the more money can be spent mining, leading to an increase in security and an increase in the value of the network. Each block that is added to the blockchain, starting with the block containing a given transaction, is called a confirmation of that transaction. An Analysis of Google Search Data". Retrieved double spending attack bitcoin calculator January

Archived from the original on 3 November International Association for Cryptologic Research. Bitcoin mining is a competitive endeavor.
Retrieved 18 October Hashes look random compared with the data put in. Economic and Environmental Costs of Bitcoin Mining".
Upon reconnection, a node downloads and verifies new blocks from other nodes to complete its local copy of the blockchain. Double spending attack bitcoin calculator 13 February The only conclusion we can draw from this comparison is that Silk Road-related trades could plausibly correspond to 4. Theoretically, the more valuable the tokens become, the more money can be spent mining, leading to an increase in security and an increase in the value of the network.

Retrieved 23 December Retrieved 14 January According to the Internet Watch Foundationa UK-based charity, bitcoin is used double spending attack bitcoin calculator purchase child pornography, and almost such websites accept it as payment. If Eve offers to pay Alice a bitcoin in exchange for goods and signs a corresponding transaction, it is still possible that she also creates a different transaction at the same time sending the same bitcoin to Bob.

