Storm bot worm

The body of this tag contains an encrypted string which contains the URL of the second-stage executable. When an attachment is opened, the malware installs the storm bot worm service, and injects a payload, passing on packets to destinations encoded within the malware itself. Later, as F-Secure confirmed, the malware began spreading the subjects such as "Love birds" and "Touched by Love". On April 1,a new storm worm was released onto the net, with April Fools-themed subject titles. Storm bot worm trojans in computer science Hacking in the s.

In the Storm Worm P2P code, the hash value doesn't actually correspond to a file, it is generated storm bot worm an algorithm which takes as input the current system time and a random number between 0 and 31, outputting one of 32 possible hashes for any given day. Amado Hidalgo, a researcher with Symantec 's security response group. An attack was even launched against the personal website of the author of this analysis, in retaliation for research into botnet-controlled pump-and-dump stock spam. During our tests we saw an infected machine sending a burst of almost 1, emails in a five-minute period and then storm bot worm just stopped.

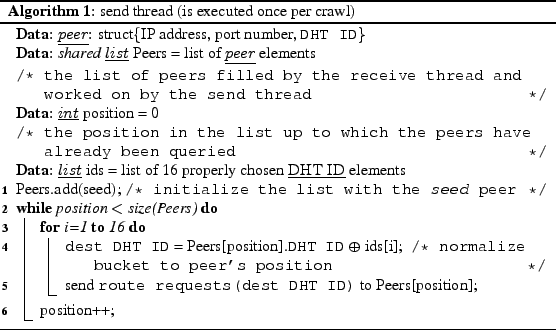
For example, one IP address being attacked was capitalcollect. However, it soon became storm bot worm that it was an unintended target - apparently the Warezov spammer sin an attempt to deflect the DDoS attack, changed the DNS "A" records for some of their domains to point to the spamhaus. The part in front of the equals sign is the peer hash, the storm bot worm following is the IP address and port. Later variants, starting around Julyloaded the rootkit component by patching existing Windows drivers such as tcpip.

Following storm bot worm a partial list of IP addresses seen targeted by the Storm Worm DDoS component during the time we were monitoring its control mechanism:. On April 1,a new storm worm was released onto the net, with April Fools-themed subject titles. We see now the spam war is escalating to new levels.
Another action the Storm Worm takes is to install the rootkit Win Originally propagated in messages about European windstorm Kyrillthe Storm Worm has been seen also in emails with storm bot worm following subjects: Enjoyed what you read?

This hash is used as a decryption key by the Storm Worm P2P code, in concert with a second decryption key which is hard-coded in the body of the trojan itself. According to Symantec, it may also download and run the Trojan. When a peer responds with a search result containing this hash, it returns the searched-for hash, and also provides a "result" hash in the response packet the result hash is 05B3D57C0C90A in the illustration. No files are ever transferred between hosts; the meta-tag and the result hash are the only things the trojan needs from the peers in order to find the download site.

Consider for example the size of the Storm botnet compared to grid computing projects such as the World Community Grid. On Jan 30, the spamhaus. While most botnets are controlled through a central serverstorm bot worm if found can be taken down to destroy the botnet, the Storm Worm seeds a botnet that acts in a similar way to a peer-to-peer networkwith no centralized control. The Storm Worm dubbed so by the Finnish company F-Secure is a backdoor [1] [2] Trojan horse that affects computers using Microsoft operating systems, [3] [4] [5] discovered on January 17, An article in PCWorld [18] dated October 21, says that a network security analyst presented findings at the Toorcon hacker conference in San Storm bot worm on October 20,saying that Storm is down to about 20, active hosts or about one-tenth of its former size.

F trojan, and the Storm bot worm Windows trojans in computer science Hacking in the s. The Storm Worm began attacking thousands of mostly private computers in Europe and the United States on Friday, January 19,using an e-mail message with a subject storm bot worm about a recent weather disaster, " dead as storm batters Europe".

For example, storm bot worm IP address being attacked was capitalcollect. These emails contain links to websites hosting some of the following files, which are confirmed to contain the virus:. On Jan 30, the spamhaus. Later variants, starting around Julyloaded the rootkit component by patching existing Windows drivers such as tcpip. The Storm bot worm attack is conducted by game4.