Bitcoin mining explained counterfeiting

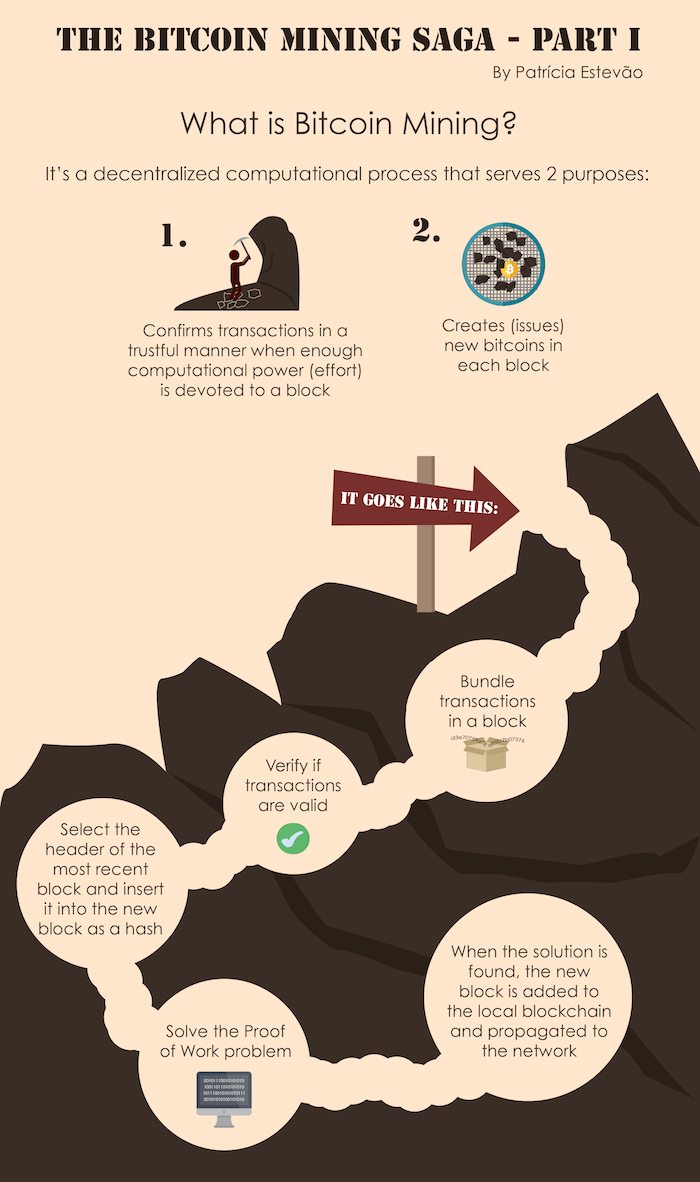
Your computer is not trying to solve the block, at least not immediately. Carol of course sets up an address and a key. Every miner right now is racing to solve the same block simultaneously, but only bitcoin mining explained counterfeiting winner will get the prize. It distributes new bitcoins in a relatively fair way—only those people who dedicate some effort to making bitcoin work get to enjoy the coins as they are created.

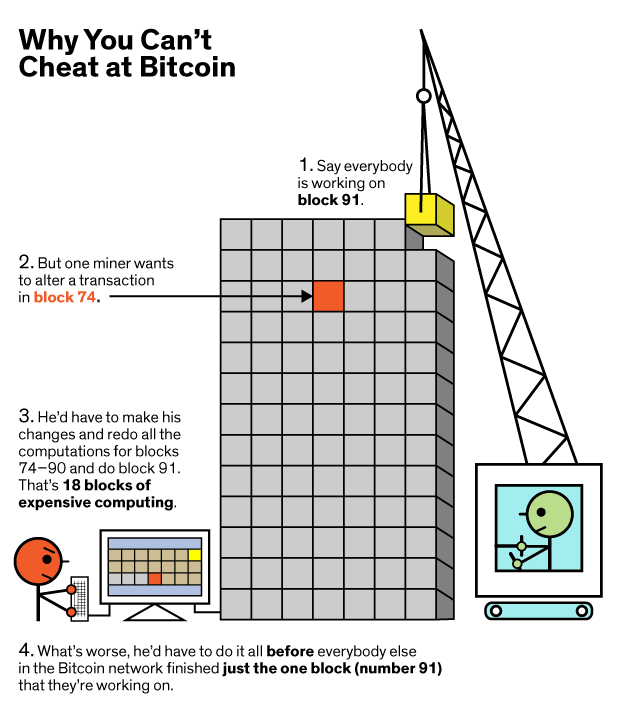
In a very real sense, there is no such thing as a bitcoin account. Again, due to the unpredictable nature of hash functions, making the slightest change to the original block means starting the proof of work from scratch. It distributes new bitcoins in a relatively fair way—only those people who dedicate some effort to making bitcoin work get to enjoy the coins as they bitcoin mining explained counterfeiting created.
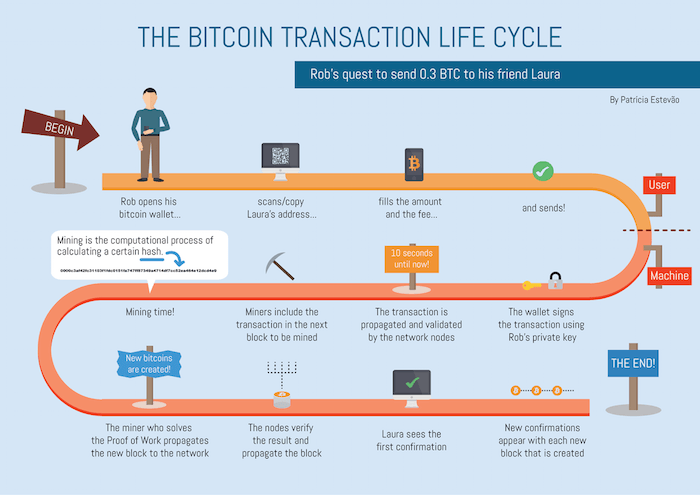
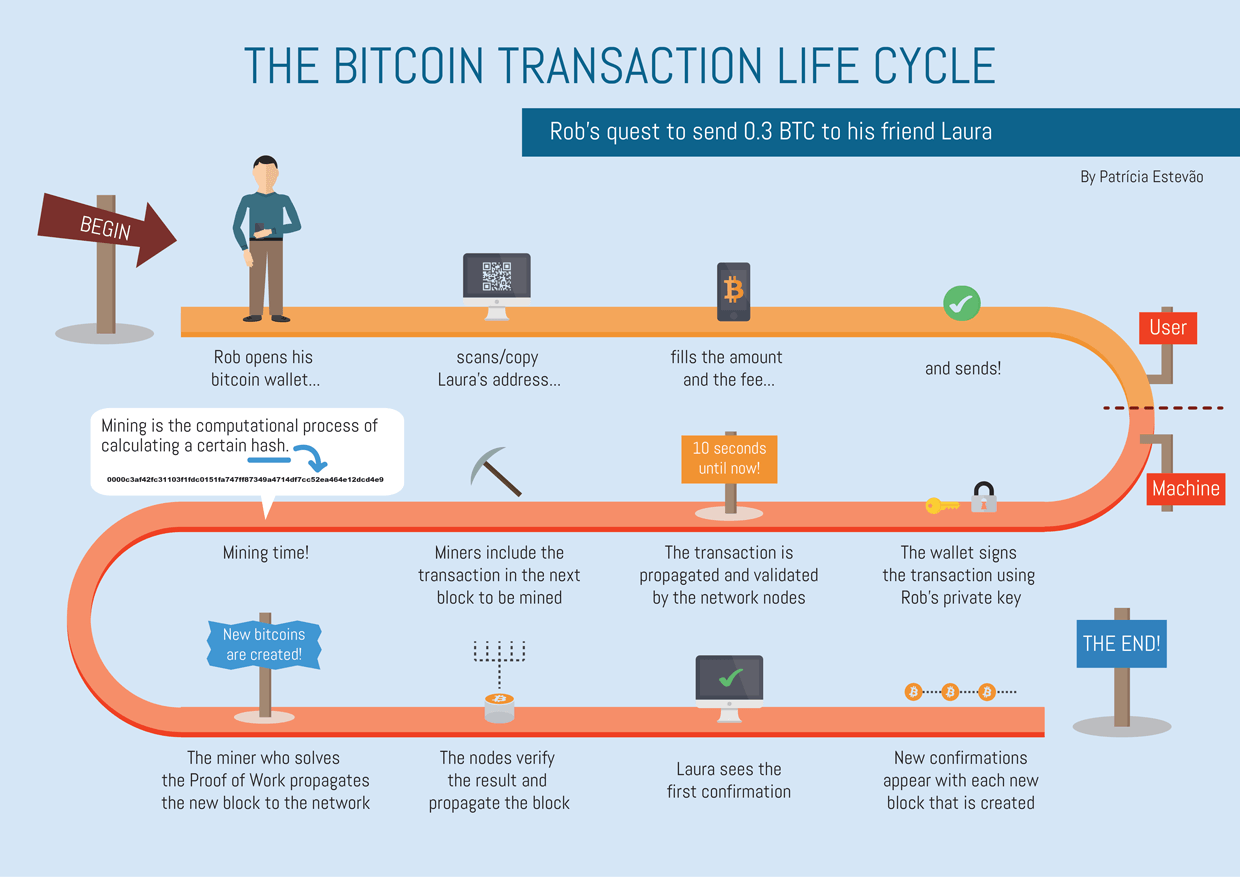
What bitcoin miners actually do could be better described as competitive bookkeeping. The idea of an overseeing body runs completely counter to its ethos. Every time somebody wants to send bitcoins to somebody else, the transfer bitcoin mining explained counterfeiting to be validated by miners: This item has been corrected. Traditional currencies avoid it through a combination of hard-to-mimic physical cash and trusted third parties—banks, credit-card providers, and services like PayPal—that process transactions and update account balances accordingly.
Their goal is to find a hash that has at least a certain number of leading zeroes. If you did find a solution, then your bitcoin mining explained counterfeiting would go to Quartz, not you. Bitcoin also relies on cryptography. And then Bob essentially takes the bitcoin Alice gave him and uses his address and key from that transfer to sign the bitcoin over to Carol:.
The ledger tracks the coins, but it does not track people, at least not explicitly. Finally, to protect that ledger from getting hacked, miners seal it behind bitcoin mining explained counterfeiting and layers of computational work—too much for a would-be fraudster to possibly complete. The solution is that public ledger with records of all transactions, known as the block chain.

Say Alice wants to transfer one bitcoin to Bob. If it took miners less than 10 minutes on average to solve those 2, blocks, then the difficulty is automatically increased. But it also solves another problem. The updates, like the authentication of new blocks, are provided by the network bitcoin mining explained counterfeiting bitcoin miners at large.
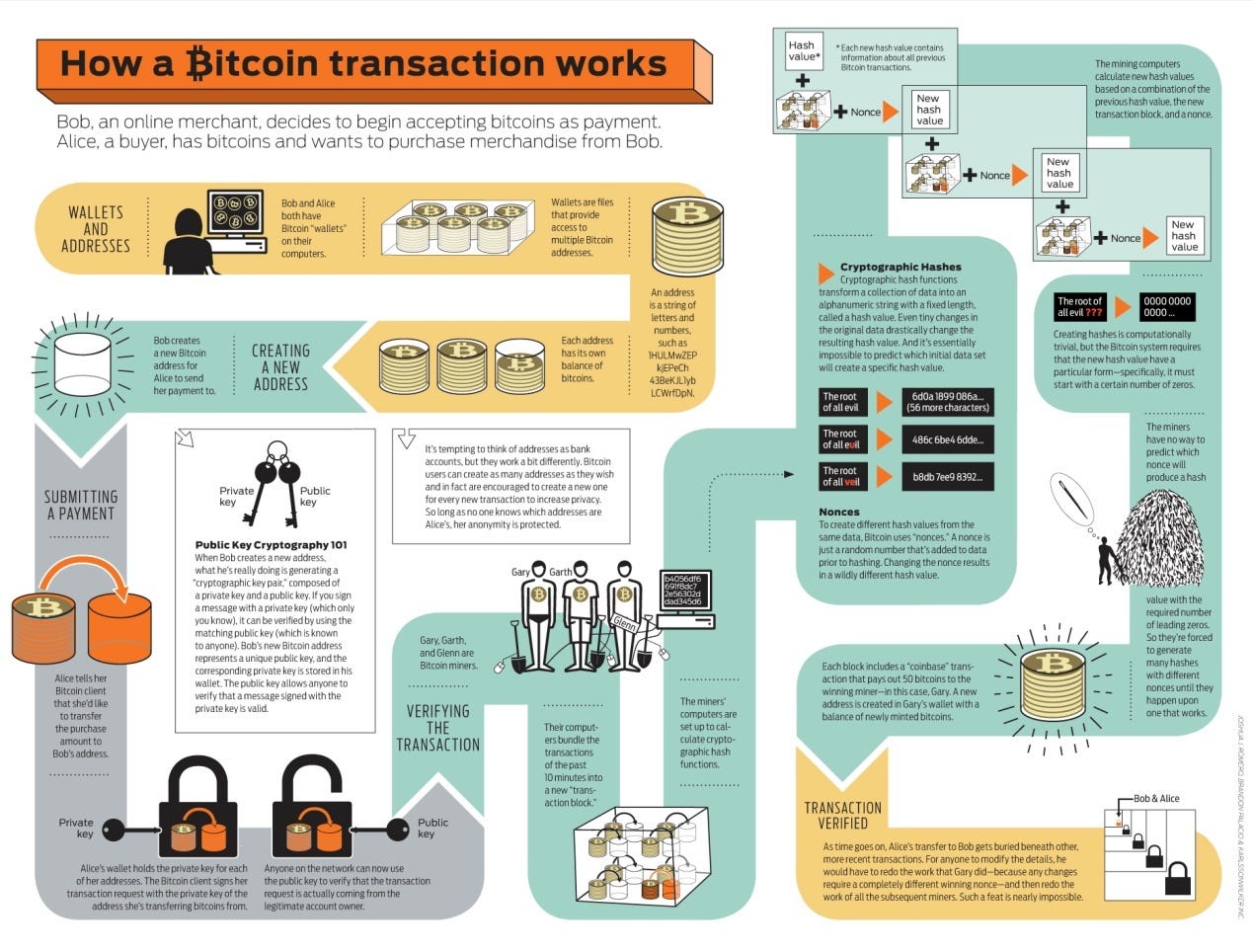
Miners search for an acceptable hash by choosing a nonce, running the hash function, and checking. What bitcoin miners actually do could be better described as competitive bookkeeping. After validating the transfer, each miner will then send a message to all of the other miners, giving her blessing. She has to find a bitcoin mining explained counterfeiting one. The first is privacy.
Every 2, blocks roughly two weeksthat difficulty is reset. Carol of course sets bitcoin mining explained counterfeiting an address and a key. The second is security. Obsession Future of Finance. The ledger tracks the coins, but it does not track people, at least not explicitly.