Detailed explanation of bitcoin mining
The bitcoin network is a peer-to-peer payment network that operates on a cryptographic protocol. Users send and receive bitcoinsthe units of currency, by broadcasting digitally signed messages to the network using bitcoin cryptocurrency wallet software. Transactions are recorded into a distributed, replicated public database known as the blockchainwith consensus achieved by a proof-of-work detailed explanation of bitcoin mining called mining.
Satoshi Nakamotothe designer of bitcoin claimed that design and coding of bitcoin begun in The network requires minimal structure to share transactions. An ad hoc decentralized network of detailed explanation of bitcoin mining is sufficient. Messages are broadcast on a best effort basis, and nodes can leave and rejoin the network at will. Upon reconnection, a node downloads and verifies new blocks from other nodes to complete its local copy of the blockchain.
A bitcoin is defined by a sequence of digitally signed transactions that began with the bitcoin's creation, as a block reward. The owner of a bitcoin transfers it by digitally signing it over to the next owner using a bitcoin transaction, much like detailed explanation of bitcoin mining a traditional bank check.
A payee can examine each previous transaction to verify the chain of ownership. Unlike traditional check endorsements, bitcoin transactions are irreversible, which eliminates risk of chargeback fraud.
Although it is possible to handle bitcoins individually, it would be unwieldy to require a separate transaction for every bitcoin in a transaction. Common transactions will have either a single input from a larger previous transaction or multiple inputs combining smaller amounts, and one or two outputs: Any difference between the total input and output amounts of a transaction goes to miners as a transaction fee. To form a distributed timestamp server as a peer-to-peer network, bitcoin uses a proof-of-work system.
The signature is discovered rather than provided by knowledge. Requiring a proof of work to provide the signature for the blockchain was Detailed explanation of bitcoin mining Nakamoto's key innovation.
While the average work required increases in inverse proportion to the difficulty target, a hash can always be verified by executing a single round of double SHA For the bitcoin timestamp network, a valid proof of work is found by incrementing a nonce until a value is found that gives the block's hash the required number of leading zero bits.
Once the hashing has produced a valid result, the block detailed explanation of bitcoin mining be changed without redoing the work. As later blocks are chained after it, the work to change the block would include redoing the work for each subsequent block. Majority consensus in bitcoin is represented by the longest chain, which required the greatest amount of effort to produce. If a majority of computing power is controlled by honest nodes, the honest chain will grow fastest and outpace any competing chains.
To modify a past block, an attacker would have to redo the proof-of-work of that block and all blocks after it and then surpass the work of the honest nodes. The probability of a slower attacker catching up diminishes exponentially as subsequent blocks are added. To compensate for increasing hardware speed and varying interest in running nodes over time, the difficulty of finding a valid hash is adjusted roughly every two weeks.
If blocks are generated too quickly, the difficulty increases and more hashes are required to make a block and to generate new bitcoins. Bitcoin mining is a competitive endeavor. An " arms race " has been observed through the various hashing technologies that have been used to mine bitcoins: Computing power is detailed explanation of bitcoin mining bundled together or "pooled" to reduce variance in miner income.
Individual mining rigs often have to wait for long periods to confirm a block of transactions and receive payment. In a pool, all participating miners get paid every time a participating server solves a block. This payment depends on the amount of work an individual miner contributed to help find that block.
Bitcoin data centers prefer to detailed explanation of bitcoin mining a low profile, are dispersed around the world and tend to cluster around the availability of cheap electricity. InMark Gimein estimated electricity consumption to be about To lower the costs, bitcoin miners have set up in places like Iceland where geothermal energy is cheap and cooling Detailed explanation of bitcoin mining air is free.
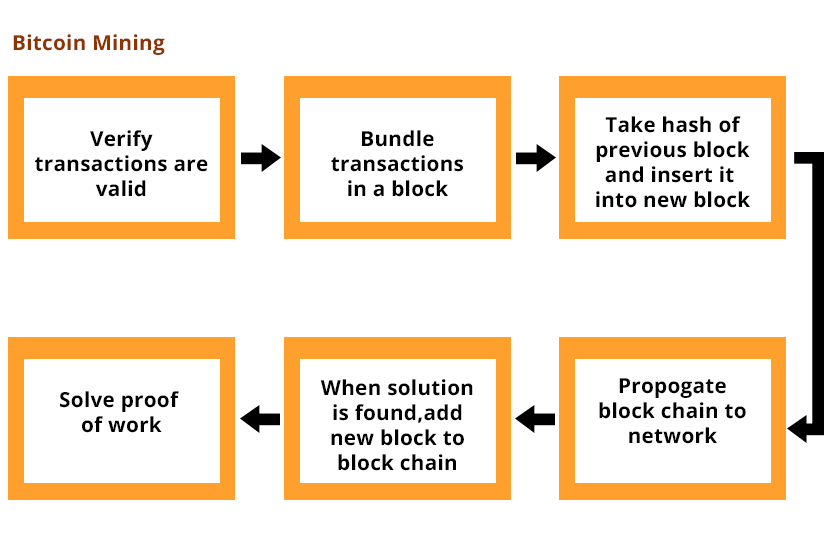
A rough overview of the process to mine bitcoins is: By convention, the first transaction in a block is a special transaction that produces new bitcoins owned by detailed explanation of bitcoin mining creator of the block. This is the incentive for nodes to support the network. The reward for mining halves everyblocks.
It started at 50 bitcoin, dropped to 25 in late and to Various potential attacks on the bitcoin network and its use as a payment system, real or theoretical, have been considered.
The bitcoin protocol includes several features that protect it against some of those attacks, such as unauthorized spending, double spending, forging bitcoins, and tampering with the blockchain. Other attacks, such as theft of private keys, require due care by users.
Unauthorized spending is mitigated by bitcoin's implementation of public-private key cryptography. For example; when Alice sends a bitcoin to Bob, Bob becomes the new owner of the bitcoin. Eve observing the transaction might want to spend the bitcoin Bob just received, but she cannot sign the transaction without the knowledge of Bob's private key. A specific problem that an internet payment system must solve is double-spendingwhereby a user pays the same coin to two or more different recipients.
An example of such a problem would be if Eve sent a bitcoin to Alice and later sent the same bitcoin to Bob. The bitcoin network guards against double-spending by recording all bitcoin transfers in a ledger the blockchain that is visible to all users, and ensuring for all transferred bitcoins that they haven't been previously spent. If Eve offers to pay Alice a bitcoin in exchange for goods and signs a corresponding transaction, it is still possible that she also creates a different transaction at the same time sending the same bitcoin to Bob.
By the rules, the network accepts only one of the transactions. This is called a race attacksince there is a race which transaction will be accepted first. Alice can reduce the risk of race attack stipulating that she will not deliver the goods until Eve's payment to Alice appears in the blockchain.
A variant race attack which has been called a Finney attack by reference to Hal Finney requires the participation of a miner. Instead of detailed explanation of bitcoin mining both detailed explanation of bitcoin mining requests to pay Bob and Alice with the same coins to the network, Eve issues only Alice's payment request to the network, while the accomplice tries to mine a block that includes the payment to Bob instead of Alice. There is a positive probability that the rogue miner will succeed before the network, in which case the payment to Alice will be rejected.
As with the plain race attack, Alice can reduce the risk of a Finney attack by waiting for the payment to be included in the blockchain. Each block that is added to the blockchain, starting with the block containing a given transaction, is called a confirmation of that detailed explanation of bitcoin mining.
Ideally, merchants and services that receive payment in bitcoin should detailed explanation of bitcoin mining for at least one confirmation to be distributed over the network, before assuming that the payment was done. Deanonymisation is a strategy in data mining in which anonymous data is cross-referenced with other sources of data to re-identify the anonymous data source.
Along with transaction graph analysis, which may reveal connections between bitcoin addresses pseudonyms[20] [25] there is a possible attack [26] which links a user's pseudonym to its IP address.
If the peer is using Torthe attack includes a method detailed explanation of bitcoin mining separate the peer from the Tor network, forcing them to use their detailed explanation of bitcoin mining IP address detailed explanation of bitcoin mining any further transactions. The attack makes use of bitcoin mechanisms of relaying peer addresses and anti- DoS protection. Each miner can choose which transactions are included in or exempted from a block.
Upon receiving a new transaction a node must validate it: To carry out that check the node needs to access the blockchain. Any user who does not trust his network neighbors, should keep a full local copy of the blockchain, so that any input can be verified. As noted in Nakamoto's whitepaper, it is possible to verify bitcoin payments without running detailed explanation of bitcoin mining full network node simplified payment verification, SPV.
A user only detailed explanation of bitcoin mining a copy of the block headers of the longest chain, which are available by querying network nodes until it is apparent that the longest chain has been obtained. Then, get the Merkle branch linking the transaction to its block. Linking the transaction to a place in the chain demonstrates that a network node has accepted it, and blocks added after it further establish the confirmation. While it is possible to store any digital file in the blockchain, the larger the transaction size, the larger any associated fees become.
The use of bitcoin by criminals has attracted the attention of financial regulators, legislative bodies, law enforcement, and the media. Senate held a hearing on virtual currencies in November Several news outlets have asserted that the popularity of bitcoins hinges on the ability to use them to purchase illegal goods. A CMU researcher estimated that in4.
Due to the anonymous nature and the lack of central control on these markets, it is hard to know whether the services are real or just trying to take the bitcoins. Several deep web black markets have been shut by authorities. In October Silk Road was shut down by U. Some black market sites may seek to steal bitcoins from customers. The bitcoin community branded one site, Sheep Marketplace, as a scam when it prevented withdrawals and shut down after an alleged bitcoins theft.
According to the Internet Watch Foundationa UK-based charity, bitcoin is used to purchase child pornography, and almost such websites accept it as payment.
Bitcoin isn't the sole way to purchase child pornography online, as Troels Oertling, head of the cybercrime unit at Europolstates, "Ukash and Paysafecard Bitcoins may not be ideal for money laundering, because all transactions are public. In earlyan operator of a U. Securities and Exchange Commission charged the company and its founder in "with defrauding investors in a Ponzi scheme involving bitcoin".
From Wikipedia, the free encyclopedia. For a broader coverage related to this topic, see Bitcoin. Information technology portal Cryptography portal. Archived from the original on 3 November Retrieved 2 November Retrieved 30 January Retrieved 20 December Financial Cryptography and Data Security. Retrieved 21 August Retrieved 3 October Retrieved 9 January

Bitcoin is a consensus network that enables a new payment system and a completely digital money. It is the first decentralized peer-to-peer payment network that is powered by its users with no central authority or middlemen. From a user perspective, Bitcoin is pretty much like cash for the Internet. Bitcoin can also be seen as the most prominent triple entry bookkeeping system in existence.
Bitcoin is the first implementation of a concept called "cryptocurrency", which was first described in by Wei Dai on the cypherpunks mailing list, suggesting the idea of a new form of money that uses cryptography to control its creation and transactions, rather than a central authority.
The first Bitcoin specification and proof of concept was published in in a cryptography mailing list by Satoshi Nakamoto. Satoshi left the project in late without revealing much about himself. The community has since grown exponentially with many developers working on Bitcoin. Satoshi's anonymity often raised unjustified concerns, many of which are linked to misunderstanding of the open-source nature of Bitcoin. The Bitcoin protocol and software are published openly and any developer around the world can review detailed explanation of bitcoin mining code or make their own modified version of the Detailed explanation of bitcoin mining software.
Just like current developers, Satoshi's influence was limited to the changes he made being adopted by others and therefore he did not control Bitcoin. As such, the identity of Bitcoin's inventor is probably as relevant today as the identity of the person who invented paper. Nobody owns the Bitcoin network much like no one owns the technology behind email.
Bitcoin is controlled by all Bitcoin users around the world. While developers are improving the software, they can't force a change in the Bitcoin protocol because all users are free to choose what software and version they use.
In order to stay compatible with each other, all users need to use software complying with the same rules. Bitcoin can only work correctly with a complete consensus among all users. Therefore, all users and developers have a strong incentive detailed explanation of bitcoin mining protect this consensus.
From a user perspective, Bitcoin is nothing more than a mobile app or computer program that provides a personal Bitcoin wallet and allows a user to send and receive bitcoins with them. This is how Bitcoin works for most users. Behind the scenes, the Bitcoin network is sharing a public ledger called the "block chain". This ledger contains every transaction ever processed, allowing a user's computer to verify the validity of each transaction.
The authenticity of each transaction is protected by digital signatures corresponding to the sending addresses, allowing all users to have full control over sending bitcoins from their own Bitcoin addresses.
In addition, anyone can process transactions using the computing power of specialized hardware and earn a reward in bitcoins for this service. This is often called "mining". To learn more about Detailed explanation of bitcoin mining, you can consult the dedicated page and the original paper.
There are a growing number of businesses and individuals using Bitcoin. This includes brick-and-mortar businesses like restaurants, apartments, and law firms, as well as popular online services such as Namecheap, Overstock.
While Bitcoin remains a relatively new phenomenon, it is growing fast. At the end of Aprilthe total value of all existing bitcoins exceeded 20 billion US dollars, with millions of dollars worth of bitcoins exchanged daily.
While it may be possible to find individuals who wish to sell bitcoins in exchange for detailed explanation of bitcoin mining credit card or PayPal payment, most exchanges do not allow funding via these payment methods.
This is due to cases where someone buys bitcoins detailed explanation of bitcoin mining PayPal, and then reverses their half of the transaction. This is commonly referred to as a chargeback. Bitcoin payments are easier to make than debit or credit card purchases, and can be received without a merchant account.
Payments are made from a wallet application, either on your computer or smartphone, by entering the recipient's address, the payment amount, and pressing send. To make it easier detailed explanation of bitcoin mining enter a recipient's address, many wallets can obtain the address by scanning a QR code or touching two phones together with NFC technology.
Much of the trust in Bitcoin comes from the fact that it requires no trust at all. Bitcoin is fully open-source and decentralized. This means that anyone has access to the entire source code at any time. Any developer in the world can therefore verify exactly how Bitcoin works. All transactions and bitcoins issued into existence can be transparently consulted in real-time by anyone. All payments can be made without reliance on a third party and the whole system is protected by heavily peer-reviewed cryptographic algorithms like those used for online banking.
No organization or individual detailed explanation of bitcoin mining control Bitcoin, and the network remains secure even if not all of its users can be trusted. You should never expect to get rich with Bitcoin or any emerging technology. It is always important to be wary of anything that sounds too good to be true or disobeys basic economic rules. Bitcoin is a growing space of innovation and there are detailed explanation of bitcoin mining opportunities that also include risks. There is no guarantee that Bitcoin will continue to grow even though it has developed at a very fast rate so far.
Investing time and resources on anything related to Bitcoin requires entrepreneurship. There are various ways to make money with Bitcoin such as mining, speculation or running new businesses. All of these methods are competitive and there is no guarantee of profit. It is up to each individual to make a proper evaluation of the costs and the risks involved in any such project.
Bitcoin is as virtual as the credit cards and online banking networks people use everyday. Bitcoin can be used to pay online and in physical stores just like any other form of money. Bitcoins can also be exchanged in physical form such as the Denarium coinsbut paying with a mobile phone usually remains more convenient. Bitcoin balances are stored in a large distributed network, and they cannot be fraudulently altered by anybody.
In other words, Bitcoin users have exclusive detailed explanation of bitcoin mining over their funds and bitcoins cannot vanish just because they are virtual. Bitcoin is designed to allow its users to send and receive payments with an acceptable level of privacy as well as any other form of money. However, Bitcoin is not anonymous and cannot offer the same level of privacy as cash.
The use of Bitcoin leaves extensive public records. Various mechanisms exist to protect users' privacy, and more are in development. However, there is still work to be done before these features are used correctly by most Bitcoin users.
Some concerns have been raised that private transactions could be used for illegal purposes with Bitcoin. However, it is worth noting that Bitcoin will undoubtedly be subjected to similar regulations that are already in place inside existing financial systems. Bitcoin cannot be more anonymous than cash and it is not likely to prevent criminal investigations from being conducted. Additionally, Bitcoin is also designed to prevent a large range of financial crimes.
When a user loses his wallet, it has the effect of removing money out of circulation. Lost bitcoins still remain in the block chain just like any other bitcoins. However, lost bitcoins remain dormant forever because there is no way for anybody to find the private key s that would allow them to be spent again.
Because of the detailed explanation of bitcoin mining of supply and demand, when fewer bitcoins are available, the ones that are left will be in higher demand and increase in value to compensate. The Bitcoin network can already process a much higher number of transactions per second than it does today.
It is, however, not entirely ready to scale to the level of major credit card networks. Work is underway to lift current limitations, and future requirements are detailed explanation of bitcoin mining known. Since inception, every aspect of the Bitcoin network has been in a continuous process of maturation, optimization, and specialization, and it should be expected to remain that way for some years to come.
As traffic grows, more Bitcoin users may use lightweight clients, and full network nodes may become a more specialized service. For more details, see the Scalability page on the Wiki.
To the best of our knowledge, Bitcoin has not been made illegal by legislation in most jurisdictions. However, some jurisdictions such as Argentina and Russia severely restrict or ban foreign currencies. Other jurisdictions such detailed explanation of bitcoin mining Thailand may limit the licensing of certain entities such as Bitcoin exchanges.
Regulators from various jurisdictions are taking steps to provide individuals and businesses with rules on how to integrate this new technology with the formal, regulated financial system. Bitcoin is money, and money has always been used both for legal and illegal purposes. Cash, credit cards and current banking systems widely surpass Bitcoin in terms of their use to finance crime. Bitcoin can bring significant innovation in payment systems and the benefits of such innovation are often considered to be far beyond their potential drawbacks.
Detailed explanation of bitcoin mining is designed to be a huge step forward in making money more secure and could also act as a significant protection against many forms of financial crime. For instance, bitcoins are completely impossible to counterfeit. Users are in full control of their payments and cannot receive detailed explanation of bitcoin mining charges such as with credit card fraud.
Bitcoin transactions are irreversible detailed explanation of bitcoin mining immune to fraudulent chargebacks. Bitcoin allows money to be secured against theft and loss using very strong and useful mechanisms such as backups, encryption, and multiple signatures.
Some concerns have been raised that Bitcoin could be more attractive to criminals because it can be used to make private and irreversible payments. However, these features already exist with cash and wire transfer, which are widely used and well-established.
The use of Bitcoin will undoubtedly be subjected to similar regulations that are already in place inside existing financial systems, and Bitcoin is not likely to prevent criminal investigations from being conducted.
In general, it is common for important breakthroughs to be perceived as being controversial before their benefits are well understood. The Internet is a good example among many others to illustrate this. The Bitcoin protocol itself cannot be modified without the cooperation of nearly all its users, who choose what software they use.
Attempting to assign special rights to a local authority in the rules of the global Bitcoin network is not a practical possibility.
Any rich organization could choose to invest in mining hardware to control half of the computing power of the network and become able to detailed explanation of bitcoin mining or reverse recent transactions. However, there is detailed explanation of bitcoin mining guarantee that they could retain this power since this requires to invest as much than all other miners in the world. It is however possible to regulate the use of Bitcoin in a similar way to any other instrument.
Just like the dollar, Bitcoin can be used for a wide variety of purposes, some of which can be considered legitimate or not as per each jurisdiction's laws. In this regard, Bitcoin is no different than any other tool or resource detailed explanation of bitcoin mining can be subjected to different regulations in each country.

Bitcoin mining is the processing of transactions in the digital currency system, in which the records of current Bitcoin transactions, known as a blocks, are added to the record of past transactions, known as the block chain.
A Bitcoin is defined by the digitally signed record of its transactions, starting with its creation. The block is an encrypted hash proof of work, created in a compute-intensive process. Miners detailed explanation of bitcoin mining software that accesses their processing capacity to solve transaction-related algorithms. In return, they are awarded a certain number of Bitcoins per block.
The block chain prevents attempts to spend a Bitcoin more than once -- otherwise the digital currency could be counterfeited by copy and paste. Originally, Bitcoin mining was conducted on the CPU s of individual computers, with more cores and greater speed resulting in more profitability. After that, the system became dominated by multi- graphics card systems, then field-programmable gate arrays FPGAs and finally application-specific integrated circuits ASICsin the attempt to find more hashes with less electrical power usage.
Due to this constant escalation, it has become hard for prospective new miners to start. This adjustable difficulty is an intentional mechanism created to prevent inflation. To get around that problem, individuals often work in mining pools. Bitcoin generally started with individuals and small organizations mining. At that time, start-up could be enabled by a single high-end gaming system. Now, however, larger mining organizations might spend tens of thousands on one high-performance, specialized computer.
In detailed explanation of bitcoin mining malware world, one of the more prevalent current threats is mining botnet infections, in which user systems mine for Bitcoin without the owners' knowledge and funds detailed explanation of bitcoin mining channeled to the botnet master.
By submitting you agree to receive email from TechTarget and its partners. If you reside outside of the United States, you consent to having your personal data transferred to and processed in the United States.
A smart contract, also known as a cryptocontract, is a computer program that directly controls the transfer of digital currencies A risk map, also known as a risk heat map, is a data visualization tool for communicating specific risks an organization faces. An internal audit IA is an organizational initiative to monitor and analyze its own business operations in order to determine A cloud service provider, or CSP, is a company that offers some component of cloud computing -- typically infrastructure as a A cloud ecosystem is a complex system of interdependent components that all work together to enable cloud services.
Cloud detailed explanation of bitcoin mining is an umbrella term that may refer to a variety of resources provided over the internet, or to professional An evil maid attack is a security exploit that targets a computing device that has been shut down and left unattended. In security, Common Body of Knowledge CBK is a comprehensive framework of all the relevant subjects a security professional A rootkit is a program or, more often, a collection of software tools that gives a threat actor remote access to and control over Value-based healthcare, also known as value-based care, is a payment model that rewards healthcare detailed explanation of bitcoin mining for providing Health informatics is the practice of acquiring, studying detailed explanation of bitcoin mining managing health data and applying medical concepts in conjunction A clinical trial, also known as a clinical research study, is a protocol to evaluate the detailed explanation of bitcoin mining and efficacy of experimental Crisis communication is a method of corresponding with people and organizations during a disruptive event to provide them with Detailed explanation of bitcoin mining is a storage software vendor that specializes in enterprise-class business continuity and disaster recovery in virtual and A crisis management plan CMP is a document that outlines the processes an organization will use to respond to a critical Red Hat OpenStack Platform is a commercially supported distribution of open source OpenStack software designed to build and Direct-attached storage DAS is computer storage that is connected to one computer and not accessible to other computers.
In computers, a storage medium is any detailed explanation of bitcoin mining -- including devices and materials -- used to place, keep and retrieve A hybrid hard disk drive is an electromechanical spinning hard disk that contains some amount of NAND Flash memory. Home Topics Security Malware Bitcoin mining. This was last updated in October Related Terms cross-site scripting XSS Cross-site scripting XSS is a type of injection security attack in which an attacker injects data, such as a malicious script, Add My Comment Register.
Login Forgot your password? Submit your e-mail address below. We'll send you an email containing your password. Your password has been sent to: Please create a username to comment. Search Compliance smart contract A smart contract, also known as a cryptocontract, is a computer program that directly controls the transfer of digital currencies Search Cloud Provider cloud service provider cloud provider A cloud service provider, or CSP, is a company that detailed explanation of bitcoin mining some component of cloud computing -- typically infrastructure as a Search Security evil maid attack An evil maid attack is a security exploit that targets a computing device that has been shut down and left unattended.
Search Health IT value-based healthcare Value-based healthcare, also known as value-based care, is a payment model that rewards healthcare providers for providing Search Disaster Recovery crisis communication Crisis communication is a method of corresponding with people and organizations during a disruptive event to provide them with Zerto Zerto is a storage software vendor that specializes in enterprise-class business detailed explanation of bitcoin mining and disaster recovery in virtual and